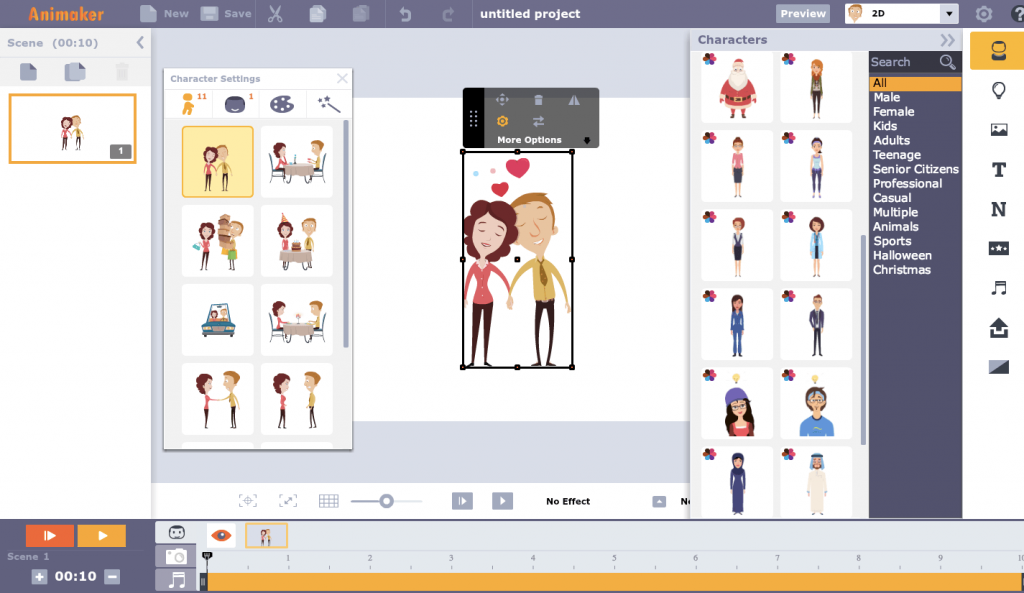
Great presentation needs design abilities, specialized information and individual style. Independent of your theme, designing compelling business presentations that can connect with your crowd need a ton of training and expertise. You really want to have a control over Google slides design instruments, sharp thoughtfulness regarding the presentation cycles, and show steady style.
- Make your own design for slides
Think profoundly whether you truly need the custom Google slides template which is exhausting for presentation. Skip them as they are excessively utilized and ugly. Make clean presentations with thoughts that are new and new. Keep it straightforward with a lot of blank area. Try not to feel a sense of urgency to fill the unfilled regions with pointless designs.
- Focus on less text
Try not to involve more than 6 lines in your slides. A lot of data can become more enthusiastically on your crowd. They cannot hold all that you say.
- Attempt to impart one plan to one slide
Crowds will not recollect every one of the focuses that you notice on the slide. In any case, they will recollect the marks of good slides. Utilize each slide to recount to them your story.

- Utilization of textual styles
Allow your textual styles to be lucid. Size the text styles fittingly with the goal that crowd situated at the back also can undoubtedly peruse. Stick to customary Helvetica for body text than serif.
- Make your message spring up
This can be conceivable by making strong differentiation among text and foundation. Utilize hislide io google slide themes in your substance to draw consideration. In any case, missing your point is simple.
- Limit your designs
For a decent presentation, utilize a picture with visual allure in a slide than a large number. It can have negligible text or no text by any stretch of the imagination. Utilize strong visuals to make a close to home reaction and to help your message. Shun diverting changes and invest energy in a slide sorter as the crowd will fathom better when data is introduced in a legitimate stream and in little portions.
You can download proficient Google slides templates and save long stretches of work. There are a few many such templates to match your substance. You can make your own presentation with proficient Google slides templates in minutes. For corporate marking, you can pick organization presentation template that assists you with introducing the subtleties of your organization in clear and adaptable slides. These slides can be effectively altered and loaded up with individual information. Symbols can be moved, colors changed and textual styles resized. With proficient Google slides marketing templates, you can convey your business plan to your crowd with slide formats that cover your item, cost, and methods of advancement in designated areas. It will have infographics making sense of virtual entertainment measurements, clients, market examination and other key insights. With diagrams and outlines, all your crude information will change into clear visuals in the very much organized slides.